GitHub Action¶
stacklet/sinistral-action is
a turnkey GitHub Action that scans Infrastructure as Code in your repository
against your Sinistral project's policies. It wraps the
sinistral-cli so you don't need
to install or configure it yourself.
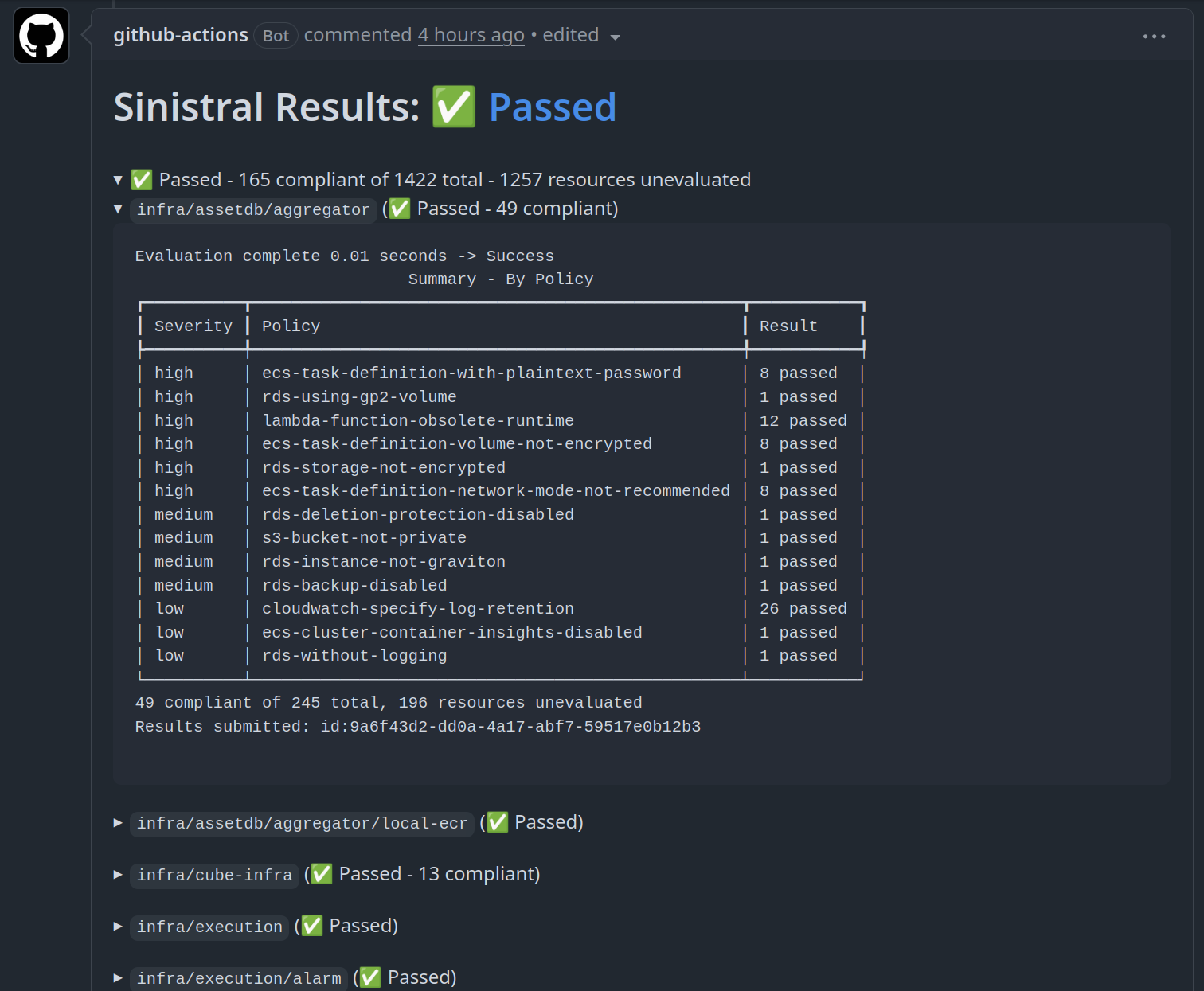
- Pull requests — results are posted (and updated in place) as a PR comment.
- Push — results appear in the Actions log.
- Failure — the action exits non-zero on policy violations, suitable for use with branch protection rules.
For lower-level CI integrations (other CI systems, custom pipelines, or Organization Credentials), see CI Usage.
Prerequisites¶
- A Sinistral project. See Getting Started.
- Project Credentials for that project, stored as GitHub Actions secrets. See Project Credentials for how to obtain them.
Usage¶
Add the following workflow to .github/workflows/sinistral.yaml:
name: IaC
on:
push:
branches: [main]
pull_request:
branches: [main]
jobs:
sinistral:
runs-on: ubuntu-latest
permissions:
contents: read
pull-requests: write # Required for posting PR comments
steps:
- uses: actions/checkout@v6
with:
persist-credentials: false
- uses: stacklet/sinistral-action@v1
with:
sinistral_api_url: https://api.sinistral.example.com
sinistral_auth_url: https://auth.console.example.com
sinistral_project_client_id: ${{ secrets.SINISTRAL_CLIENT_ID }}
sinistral_project_client_secret: ${{ secrets.SINISTRAL_CLIENT_SECRET }}
sinistral_project: MyProject
iac_directories: terraform
Multiple directories¶
iac_directories accepts a newline-separated list:
Recursive scanning¶
To discover all subdirectories containing .tf files automatically:
Inputs¶
| Input | Required | Default | Description |
|---|---|---|---|
sinistral_api_url |
Yes | — | Base URL of your Sinistral API. |
sinistral_auth_url |
Yes | — | Auth URL for your Sinistral instance. |
sinistral_project_client_id |
Yes | — | OAuth2 client ID for your Sinistral project. |
sinistral_project_client_secret |
Yes | — | OAuth2 client secret for your Sinistral project. |
sinistral_project |
Yes | — | Sinistral project name to scan against. |
iac_directories |
Yes | — | Path(s) to IaC folders relative to the repo root. Newline-separated. |
recurse |
No | false |
Recursively discover subdirectories containing .tf files. |
sinistral_cli_version |
No | Pinned release | Git ref (tag, branch, SHA) of sinistral-cli. |
Permissions¶
The pull-requests: write permission is only required for the PR comment
feature. For push-only workflows, contents: read is sufficient.
Pinning for supply-chain integrity¶
Git tags are mutable. For production use, pin the action to a full-length commit SHA:
Tools like pinact can automate this for all actions in your workflows.